
Breaking Down SingHealth’s 2018 Security Incident
In 2018, SingHealth faced a devastating cyberattack where unidentified state actors exfiltrated the personal particulars of 1.5 million patients. The worst data breach in Singapore was said to specifically target the Prime Minister’s records as well, which shows that the attackers were sophisticated and had a very specific goal in mind.
The Why and How it Happened
At a high-level, this data leak was possible because of three main reasons:
- Lack of security awareness: Although the system employees were alerted to signs of compromise in their system, they did not understand the implications of such signs and thus, could not respond to the attack effectively.
- Incomplete security mitigations: Despite performing regular risk assessments, the security team did not understand the scope of the suggested mitigations and only implemented a subset in a piecemeal fashion. So the system was left vulnerable with weaknesses in the system architecture design and the software that was used to access patient data.
- Lack of continuous security solutions: There were no attack detection or security monitoring solutions in key areas of the system architecture.
How the Attack Unfolded
Before we delve into how the attack was conducted, let’s look further into how the SingHealth system was structured in 2017. Patient data was stored in a database within a local data center. Access to that data was granted via an application, Sunrise Clinical Manager (SCM), which is an electronic health records system. Virtualized versions of that SCM application were hosted on Citrix servers. For a doctor to access patient data, they would use a workstation that connects to one of the servers within the Citrix server cluster and access the SCM application on the virtual machine. The SCM application would send requests to its backend application server which first contacts the security server for user authentication before fetching data from the database through the database server. The architecture is shown below in Figure 1.
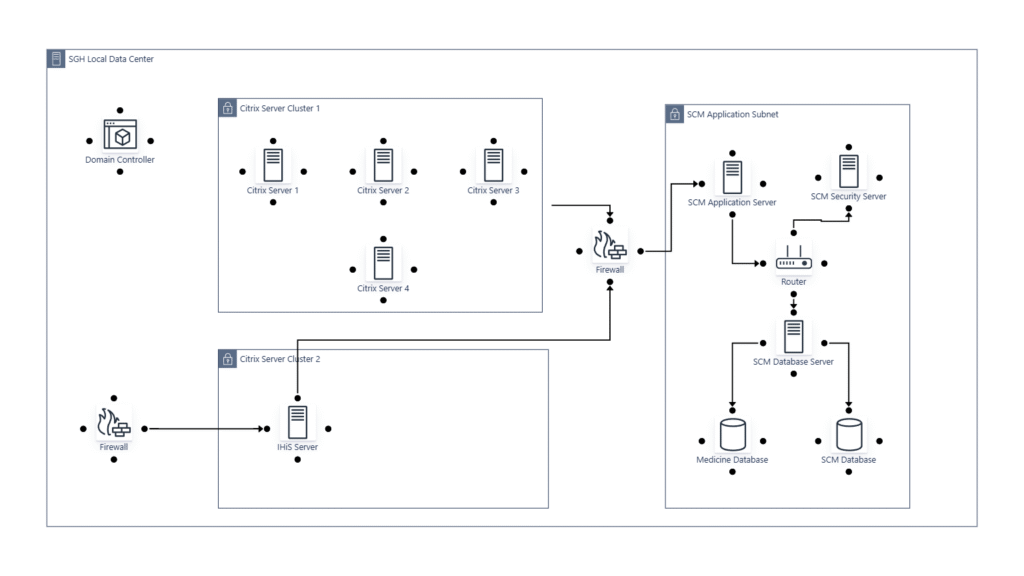
Figure 1. System architecture in 2017.
It is clear that a firewall that should be placed in front of the Citrix server cluster to prevent network traffic originating from malicious origins. Later that year, the system moved to the cloud. However, only partial subsystems were moved. So, the unprotected Citrix server cluster still had access to the critical subsystems containing patient data. Let’s take a look at how the attack leverages this flaw to attack the system.
First, an exploit in Microsoft Outlook causes a publicly available hacking tool to be downloaded on a user’s workstation. Now that the workstation is compromised, the attacker can execute commands remotely and control the workstation to do his or her bidding. The malware installed on the workstation spreads to the Citrix servers within the cluster since those servers aren’t protected. Through a series of trial and error, the attacker tries to obtain the right administrative credential in the various servers in order to connect to the SCM Application Server. Since administrative credentials were not properly secured, the attacker was able to string a series of credentials together in order to hop from one server to the next, eventually bridging the connection between the local data center and the secured SCM Application Subnet. A flaw in the SCM application itself (which was reported and not fixed completely) also allowed the attacker to perform bulk queries in order to exfiltrate data.
Lessons Learned
Although risk assessments were conducted at least twice before the attack occurred, it is clear that the insights provided in those assessments were not properly conveyed to the system operators or comprehensively understood by the security management team. The post-mortem report concludes that risk assessment forms should not come hardcoded with a set of prepopulated threats as it would be easily ignored due to its repetitive nature. Instead, threats should be identified by taking into account system information including new knowledge of security controls (e.g., the moving of parts of the system to the cloud).
Furthermore, prioritization of risks using asset classification is simplistic and not effective as it ignores the effect of network connectivity and other relationships between the system components. Attackers who understand this flaw can exploit it by penetrating lower priority assets and moving stealthily through the system, as witnessed by the SingHealth data leak.
How ThreatMirror Can Help
Our threat modeling tool, ThreatMirror, focuses on modeling your system in order to provide more contextualized threats that are specific to your system. Instead of mapping each component to a threat, we take into account network connectivity, data flow, and system use cases in order to understand the broader picture of how attackers can move through your system in order to achieve their goal.
Moreover, risks are prioritized by looking at the entire attack path rather than singular assets. This framework ensures that an organization will focus on defending their system against the most important attack campaigns, which will provide a more holistic security posture.
For more details on how the SingHealth data leak can be deterred by good threat modeling practices, watch the video below.
References
[1] The Straits Times. Personal info of 1.5m SingHealth patients, including PM Lee, stolen in Singapore’s worst cyber attack. Published: July 20, 2018
[2] Public Report of the Committee of Inquiry into the Cyber Attack on Singapore Health Services Private Limited’s Patient Database on or around 27 June 2018. Published: Jan 10, 2019.


