UNC3886 Attack on Critical Infrastructure
UNC3886 is a hacking group that has grown in presence for targeting critical infrastructure, including telecommunications, government, technology, and defense, with a recent attack against Singapore. It’s known for targeting zero-day vulnerabilities in network and virtualization devices, particularly VMware and Fortinet, which are both common solutions used in many systems.
The Versatility of the Attack
The attack consists of two phases: seizing control of the network devices followed by manipulating the virtual machines inside hosts connected to those network devices (as shown in Figure 1 below).
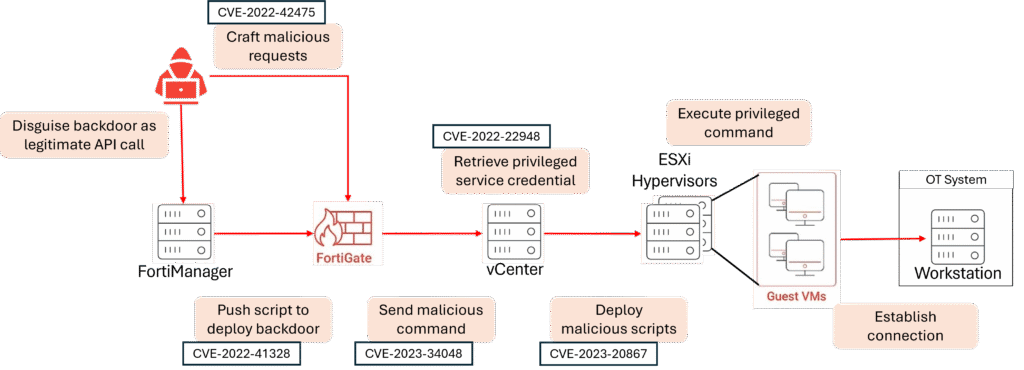
Figure 1. Workflow of UNC3886 attack
First, the attacker either compromises FortiGate firewalls directly by sending malicious requests to them, or indirectly compromises them by targeting an Internet-exposed FortiManager which then pushes malicious scripts to the firewalls.
Once inside the firewalls, the attacker uses the network access to send malicious commands to VMware’s vCenter that manages the virtual machines. From vCenter, the attacker is able to gain control of the solution and remotely connect to the virtual machines to execute the attacker’s commands. Since virtual machines are commonly used as a stepping stone to connect to internal systems, the attacker is now free to hop into the secured internal system.
If those internal systems are critical infrastructure systems, the attacker could cause power outages, transportation breakdown, and bring about broader economic harm. Moving laterally from the IT to the OT system is not new but exploiting such commonly used third-party solutions make it a particularly concerning attack.
Threat Modeling Supply Chain Compromise Attacks
The UNC3886 attack demonstrates that it is not enough to threat model the software and services developed internally by an organization. It is crucial to take into account the third-party solutions used throughout the system – from the network to the operating system to the software libraries and programs – in order to build a comprehensive threat model. In that way, an organization would be made aware of the risks of supply chain compromise attack from the very start and plan their security controls such that there are overlapping defenses in place to ensure that an attack is caught before it makes its way to the crown jewels.
In ThreatMirror, we model these threats by modeling complex systems as reusable component models that is adaptable to threats posed by different third-party solutions. Our flexibility makes it scalable to model the ever-increasing landscape of third-party solutions. For more information on how we model the UNC3886 attack, watch the video below.
References
[1] Cloaked and Covert: Uncovering UNC3886 Espionage Operations. Available at: https://cloud.google.com/blog/topics/threat-intelligence/uncovering-unc3886-espionage-operations


